Why Enterprise Agentic RAG Fails Without Access Control and How elDoc Solves It

Today, many vendors and teams claim: “We have built RAG.” And in many cases, that is true – but only at a certain level. Most of these are lightweight RAG implementations: built on small datasets, tested on limited document collections, and operating without complex access structures or governance requirements. They work well for prototypes, internal demos, or simple knowledge bases.
However, enterprise environments are fundamentally different.
Organizations do not manage hundreds or thousands of documents – they operate with millions of files and often terabytes of data distributed across departments, systems, and formats. More importantly, enterprise data is not universally accessible. It is strictly governed by roles, permissions, and policies that define who can see what. Finance teams access financial records, HR manages employee data, legal works with contracts, and leadership operates on aggregated insights.
Access is not an additional feature — it is the foundation of how enterprise systems function.
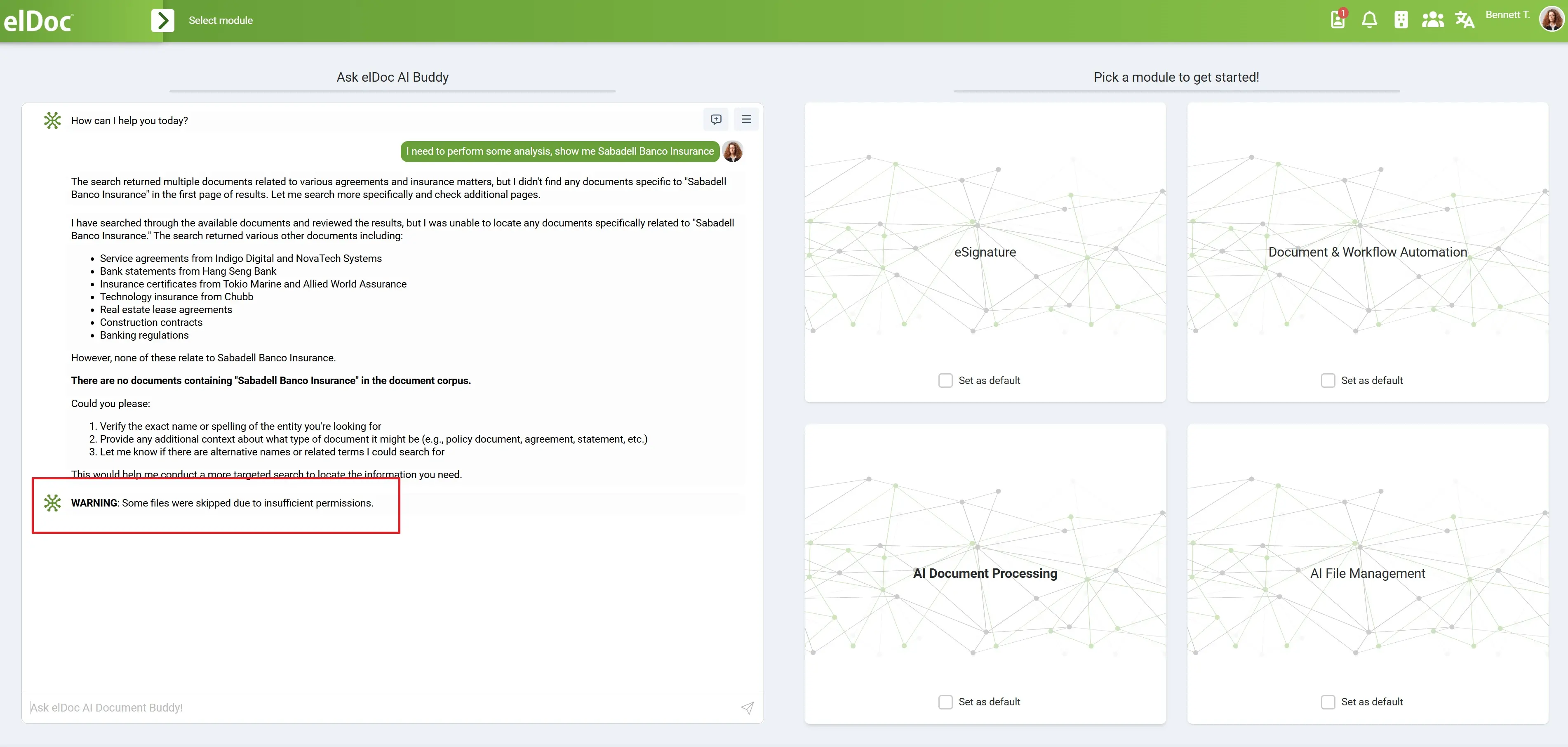
This is exactly where lightweight RAG breaks down. When applied to real enterprise data, it retrieves too much, ignores permission boundaries, mixes contexts across departments, and introduces serious risks of exposing sensitive information. Even if technically functional, such systems quickly become non-compliant, untrusted, and unusable in production environments.
This is why Agentic RAG emerges as the necessary evolution.
It goes beyond retrieval by understanding intent, planning multi-step workflows, reasoning across multiple data sources, and executing tasks automatically. It transforms AI from a passive assistant into an active system capable of driving real outcomes. But with this increased power comes a critical challenge.
Agentic RAG amplifies not only capability, but also risk. AI is no longer just retrieving information — it is combining data, making decisions, and executing actions. Without proper control, this can lead to cross-department data exposure, unauthorized data aggregation, and execution based on restricted information, resulting in compliance violations at scale.
The more powerful the system becomes, the greater the consequences of weak security.
For Agentic RAG to work in enterprise environments, access control and security must be embedded from the very first layer not added later. This means identity-aware retrieval, permission-constrained reasoning, controlled multi-step execution, and full auditability of every action.
Many organizations believe they need better models, better prompts, or better search.
In reality, what they need is:
👉 Better control
Agentic RAG is the next evolution of enterprise AI. It doesn’t just retrieve information — it plans, reasons, and executes tasks across documents and systems. But with this increased power comes greater risk.
If access control is not enforced from the start, Agentic RAG doesn’t just fail — it becomes dangerous.
The New Risk: When AI Starts Acting
Traditional RAG already introduces risk when it retrieves unauthorized data. But Agentic RAG takes this to an entirely new level.
It does not operate in a single step. It:
- Chains multiple actions together
- Combines data from different sources
- Executes workflows based on that data
This fundamentally changes the nature of the risk.
The question is no longer:
👉 “What can the AI see?”
It becomes:
👉 “What is the AI allowed to do — and with which data?”
Because once AI starts acting, not just answering, the impact of a single mistake is amplified across an entire workflow. Without strict access control, Agentic RAG can:
- Aggregate sensitive data across departments that should never be combined
- Execute workflows using restricted or confidential information
- Generate outputs that violate compliance and governance policies
- Amplify data leakage through multi-step reasoning chains
The risk scales with intelligence.
The more capable the system becomes, the greater the potential impact of uncontrolled behavior.
Why Most Agentic RAG Architectures Break
Many systems today evolve into “Agentic RAG” by simply adding orchestration layers on top of existing RAG pipelines. At a glance, this seems like progress. In reality, it often means adding autonomy on top of an already flawed foundation.
The typical pattern looks like this:
- Retrieve broadly across all available data
- Let agents reason across the results
- Execute tasks based on that reasoning
🔴 The core problem:
- Retrieval is not access-aware
- Agents are not constrained by user permissions
- Execution is not governed by enterprise rules
Even when using powerful technologies like Apache Solr for search or Qdrant for semantic understanding, the fundamental issue remains unresolved.
The system can still:
- Pull unauthorized or sensitive content
- Mix contexts across departments and access boundaries
- Act on data the user should never see or use
And when this happens within multi-step agent workflows, the consequences compound quickly.
The Core Failure
Agentic logic without access control becomes uncontrolled automation.
What starts as an intelligent system quickly turns into:
- A compliance risk
- A data governance failure
- A loss of trust in AI
Because in enterprise environments, it is not enough for AI to be smart — it must be controlled.
elDoc Enforces Access Control Before Any AI Action
In elDoc, access control is not an additional layer – it is the starting point of the entire Agentic RAG pipeline. Every request begins with identity verification and permission validation, ensuring that the system clearly understands who the user is and what they are allowed to access before any processing takes place.
This means that retrieval is not just intelligent — it is strictly permission-aware. Whether the system is querying document storage, performing full-text search via Apache Solr, or executing semantic retrieval using Qdrant, all results are pre-filtered based on access rights. Unauthorized data is never retrieved, never processed, and never exposed to the AI.
By embedding access control directly into every layer of the architecture, elDoc ensures:
- Zero exposure of restricted data
- Fully compliant retrieval across all sources
- A secure foundation for all AI-driven operations
This eliminates the root cause of failure in most Agentic RAG systems — access is enforced before intelligence is applied.
elDoc Governs Every Step of Agentic Execution
In elDoc, security does not stop at retrieval — it extends across the entire lifecycle of Agentic RAG. AI agents are capable of planning, reasoning, and executing multi-step workflows, but they operate strictly within the boundaries defined by user permissions.
Every step in an agent’s workflow is continuously controlled:
- Data used at each stage is validated against access policies
- Intermediate results cannot introduce unauthorized information
- Actions cannot be executed using restricted or cross-boundary data
This prevents “permission drift,” where sensitive data could otherwise leak through chained reasoning steps.
At the same time, elDoc ensures full transparency and control:
- Every AI action is logged
- Every data source is traceable
- Every outcome is auditable and explainable
The result is an Agentic RAG system where AI is not only powerful, but also fully governed, compliant, and trustworthy. In elDoc, agents don’t just act — they act within clearly defined and enforceable enterprise boundaries.
How elDoc Enforces Security from Day One for Agentic RAG
Security in elDoc is not something configured after deployment – it is built into the platform from the very first interaction. Every layer, from user authentication to AI execution, is designed to ensure that data remains protected, controlled, and fully governed at all times.
Identity, Authentication & Authorization — From the First Access
From day one, elDoc enforces strict identity verification and access control mechanisms:
- Multi-Factor Authentication (MFA) and OTP ensure secure user authentication
- Role-Based Access Control (RBAC) is applied with high granularity — down to the level of individual documents and even specific files
- Hierarchical permission structures allow organizations to define access across departments, business units, and roles
Critically, elDoc is designed for real enterprise dynamics:
- When a user changes roles, permissions are automatically reassigned
- When organizational structures evolve, access policies adapt instantly
- When users leave or move, access is revoked or updated in real time
👉 This ensures there are no gaps, no delays, and no risk of outdated permissions leading to data exposure.
Continuous Control, Monitoring & Auditability
Security does not stop at access — elDoc ensures continuous visibility and control over all system activity:
- Comprehensive logging of every user and AI action
- Real-time monitoring of access patterns and system behavior
- Full audit trails for compliance, investigations, and governance
Every interaction with data is:
- Traceable
- Verifiable
- Explainable
👉 This creates a fully transparent environment where organizations always know who accessed what, when, and how.
Data Protection Built Into the Platform
elDoc applies multiple layers of data protection to safeguard sensitive information:
- End-to-end data encryption (at rest and in transit)
- Watermarking and document protection mechanisms
- Strict prevention of data leakage to external or public AI services
This ensures that even when data is accessed legitimately, it remains protected against misuse or unauthorized distribution.
Enterprise-Grade Infrastructure & Resilience
Security also means reliability and availability. elDoc is designed to support mission-critical enterprise environments:
- High-availability architecture for continuous operation
- Disaster recovery readiness to protect against failures
- Support for on-premise, hybrid, or fully isolated deployments
👉 This allows organizations — especially those handling sensitive or regulated data — to operate in fully controlled and secure environments.
Agentic RAG Built for Trust, Control, and Real Enterprise Use
Enterprise AI is not just about intelligence — it is about trust, control, and accountability. Agentic RAG introduces a new level of capability: systems that don’t just retrieve information, but plan, reason, and execute across enterprise data. However, without security at its core, this power becomes a risk rather than an advantage.
That is where elDoc stands apart. Security is not treated as an add-on or a later phase. It is embedded into every layer of the platform from day one — from identity and access control, to permission-aware retrieval, to governed agent execution and full auditability.
👉 This is what makes Agentic RAG not only powerful — but truly enterprise-ready.
Let's get in touch
Explore Agentic RAG with elDoc. Request Demo or Community Version
Get your questions answered or schedule a demo to see our solution in action — just drop us a message
